Meltdown And Spectre CPU Flaws Must Be Addressed NOW

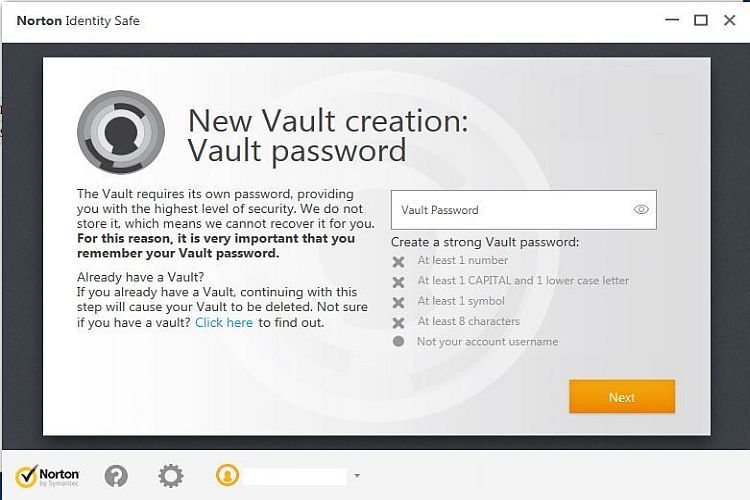
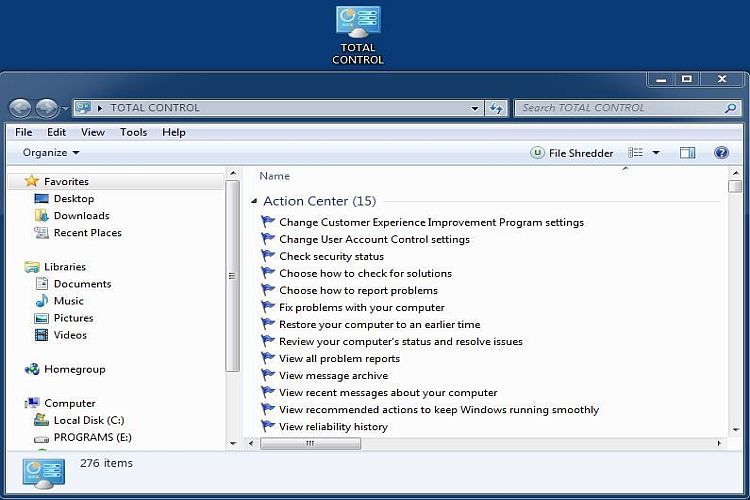
The image above is that of a CPU in a system I was recently working on and it might be a victim of either the Meltdown or Spectre exploits. This is NOT limited to Intel processors and in fact it involves AMD, ARM and Qualcomm processors and likely even more. The potential impact of these vulnerabilities is not to be underestimated. This might be scarier than any ransomware yet released because these vulnerabilities can affect the core operation of almost any computer and the exact method of corrective action appears to be elusive. It's not about Windows, not about IOS, not about Linux; it is rather about the majority of central processing units that exist today no matter what software is involved.THAT means your computer's CPU (processor for short) - or even that of your smartphone - may well be the victim in these cases as opposed to whatever software that CPU is handling. Given the likely scope of impact it's rather clear that Meltdown and Spectre CPU flaws must be addressed NOW.
The Meltdown and Spectre CPU flaws basically caught the industry off guard. Hardware vulnerability just isn't in the forefront of any development scheme because it is software which is typically exploited. The exploits themselves are scary in that almost any data can be gathered from the system kernel and that includes things such as passwords stored in Internet browsers. One other scary thing is that in an interview with Data Center Knowledge, Red Hat's chief ARM architect Jon Masters stated "The reality is that it's a cross industry, cross vendor issue that affects pretty much every architecture. It's not just Intel, AMD and ARM, it's actually every modern architecture." Intel issued a statement basically defending itself and indicating "Recent reports that these exploits are caused by a “bug” or a “flaw” and are unique to Intel products are incorrect. Based on the analysis to date, many types of computing devices — with many different vendors’ processors and operating systems — are susceptible to these exploits." This is not your average everyday exploit, it is rather a set of exploits which are very complex and in some cases hard to defend against.
These CPU flaws can be exploited because of a certain way in which processors anticipate instructions these days (yes, they're smart) called speculative execution. Meltdown and Spectre exploits can detect the CPU's altered states during this process when data becomes vulnerable and potentially gather that data. Now here's the GOOD news: Accomplishing that task is evidently not easy at all, which means that anyone trying to exploit the Meltdown or Spectre CPU vulnerabilities will have their work cut out for them. Although patching appears to patchy and it's efficiency uncertain, according to Wired.com "There hasn't been much time for extensive testing and refinement, so slapdash fixes may not offer total protection, or could create other bugs and instabilities that will need to be resolved." And more hopefully "Security researchers say that the vulnerabilities are difficult to exploit in practice, which may limit its real-world use, but a motivated and well-funded attacker could develop more efficient techniques." This means we hopefully won't see a huge exposure to exploits occurring. Wired also notes "Though possible, exploiting Meltdown and especially Spectre is complicated and challenging in practice, and some attacks require physical access. For hackers, the vulnerabilities will only get tougher to exploit as more devices start to get patched. Which means that at this point, the risk to the average user is fairly low." Let's hope that holds true. Hackers have many other ways in which they attack us trying to get passwords and other personal information and social engineering attacks like phishing have yielded results for them. See the links below for more information on the Meltdown and Spectre CPU flaws.
Intel's Response To Meltdown And Spectre Exploits
Wired Report On Meltdown And Spectre Fix
Data Center Knowledge Report On Linux Meltdown And Spectre Fix