FIREYE Discovers Major Security Breach In Microsoft’s EMET
According to Fireye this newly in the wild discovery of a variant of the Angler Exploit Kit (EK) goes beyond the usual method of just evading DEP (Data Execution Prevention) and evades Microsoft's EMET (Enhanced Mitigation Experience Toolkit) completely. In a comprehensive report released yesterday Fireye identified many exploits used by this Angler EK and how these accomplish their potentially devastating task. In fact, Fireye stated that this new security threat uses "multi-layered code obfuscation" to confuse any attempts to detect or rectify its presence along with exploits of several types.
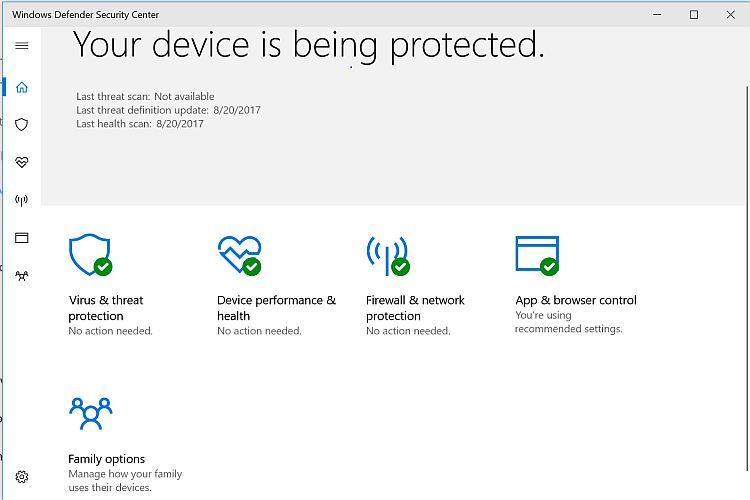
Although the Angler EK itself is not new the sophisticated level of attack this threat presents is indeed giving security experts cause to warn users and organizations to take steps toward mitigating the security vulnerabilities which it exploits. These exploits do come through web browsers and yes as always one must be certain to consistently update web browsers and their extensions, especially Flash, Java, and Microsoft Silverlight. These steps can only help to secure the computing environment in which we work, and even removing these cannot guarantee this threat would be stopped. All evidence indicates that this new threat is not to be taken lightly.
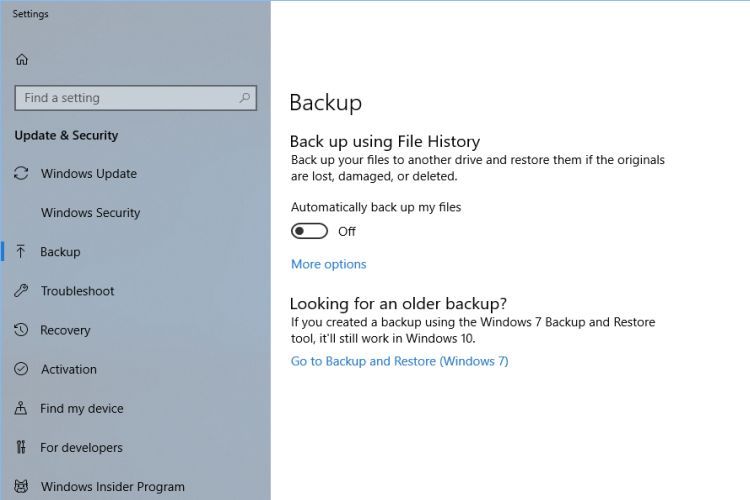
Perhaps the worst aspect of this security threat is the payload it can deliver. The TeslaCrypt ransomware. This is not a new thing either however if the TeslaCrypt ransomware the Angler EK tries to deliver is successfully executed within a computer's environment it can be more than just a headache. If you are not aware of what ransomware does it goes like this: Invade the computer's software, encrypt the majority (in most cases) of files, and demand ransom in exchange for a key to unencrypt those files. Again, more than just a headache. What you can do is make sure you do complete system backups on a regular basis (using a drive not always attached to your system) so that if you get a ransomware infection you could recover from it. It is also possible in some cases if using System Restore or System Protection that "previous versions" of files could possibly be unencrypted. Fireye's report did not indicate one way or the other on whether this is possible with this new threat. Do your due diligence and follow through with regular updates and backups to give yourself the best chance to avoid this new threat.
Read the Fireye report on Angler EK threat.